5 Tips to Secure Your cPanel Server
quick question. Do you feel confident about your current cybersecurity strategy? #
According to a study by IBM and the Ponemon Institute, the average cost of a data breach is $3.86 million.
Falling victim to a data breach can be devastating to your hosting company. Don’t make the mistake of thinking that two-factor authentication (2FA) is enough to keep your cPanel server protected. For example in November 2020, hackers exploited a vulnerability in cPanel and WebHost Manager and bypassed 2FA using brute force.
Without a good cybersecurity strategy, protection measures like two-factor authentication (2FA) are nothing more than speed bumps that slow down attackers online. But attacks can still happen – and when they do, the consequences can be devastating for your web hosting company. Not only will you deal with expensive regulatory fines and penalties, but you will also have to win back the trust of your customers. This is not easy.
Now for the good news. Keeping a cPanel server protected from data breaches and other malicious activities is not as difficult as you think. You have to make cyber security a top priority.
Here are five ways you can do just that!
5 Tips to Secure Your cPanel Server
1. Use strong passwords #
Weak passwords are easy to hack. We all know this, but not everyone follows good password practices. If your password is hacked, the rest of your online security will be compromised to a large extent.
cPanel has a password generator feature that automatically generates a secure password for you. We recommend using it if you haven’t done so already and creating a new password every month.
You can configure your server password options by editing the “/etc/login.defs” file. This way, all your password should follow your security protocol. Therefore, you avoid using generic default passwords like “admin” or “password“.
And don’t forget to enable SSL for cPanel to prevent malicious parties from snooping and finding sensitive information. You can do this by going to the “Tweak Settings” menu under “Server Configuration
2. Enhance your SSH security #
Secure Shell (SSH) is a network protocol that allows you to access a remote cPanel server. You can use this feature to manage your server from anywhere.
Here’s the thing – if you can access your server remotely, so can a designer hacker. But you can reduce their chances of success by strengthening your SSH security. Here’s how:
- Change ports: The default SSH port is 22, this is the first port attackers will try. cPanel recommends changing to any port between 1-1023 that another service is not already using.
- Restrict SSH Access: You may need to give others SSH access from time to time. Give them only the perks they need to do their work. You can do this by creating blocked shell environments.
- Run Privilege Audits: Run a audit every two months to see who has SSH access. Revoke privileges granted to anyone who no longer needs this access.
Also make sure you are using SSHv2. This is the latest version of SSH, and it offers more security than SSHv1. You can do this by editing the “/etc/ssh/sshd_config” file and changing “#Protocol 2,1” to “#Protocol 2.”
3. Update cPanel Update #
Remember that 2FA vulnerability we mentioned at the beginning of this post? The attackers were able to bypass 2FA by exploiting a bug in cPanel & WHM version 11.90.0.5. While cPanel was quick to release a patch that addressed this issue, users who did not update remained vulnerable to external threats.
Updating your cPanel will help you stay protected against flaws that could compromise your internet security.
You can update cPanel by:
WHM > cPanel > Upgrade to Latest Version
Or from the following command line:
/usr/local/cpanel/scripts/upcp
4. Using cPHulk brute force protection #
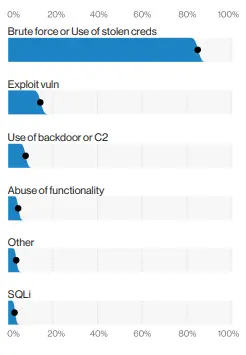
According to Verizon’s 2020 Data Breach Investigations Report, 80% of data breaches occur for two reasons:
- brute force
- Using stolen logins and passwords
Using stronger passwords is your first line of defense against brute force attacks. They make it difficult for hackers to guess your credentials. But strong passwords are not enough to protect you from determined hackers looking to gain access to your server.
This is where cPHulk can help.
cPHulk is a brute force protection tool designed to prevent hackers from guessing your security credentials. It works by blocking IP addresses that frequently enter incorrect usernames and passwords.
You can enable cPHulk through WHM > Security Center > cPHulk Brute Force Protection
There, you can set the number of failed login attempts. This will prompt cPHulk to block the IP address from your server when the number you set is exceeded.
Just be sure to add your IP address to the management whitelist if you have a static IP. This lets cPHulk know that your IP address is not being blocked if you have too many failed logins. The last thing you want is for your server to be locked because you entered the wrong password.
5. Deploying a comprehensive server protection solution #
There are several practices you can implement to enhance the security of your server. Using stronger passwords and updating your IT infrastructure will go a long way towards protecting you from cyber attacks.
But there will always be security holes popping up, and hackers will always look for ways to exploit them. The best way to reduce the risk of cyber attacks is to deploy an effective server protection suite along with the security practices listed above. This will give your server an extra layer of protection by protecting you from hackers looking to circumvent other security measures.
Get the protection you deserve with Hyyat Host and premium server management plans to review
Best Regards, Hyyat Host Team